Experts hack power grid in no time
SOURCE
Hackers Target U.S. Power Grid
Government Quietly Warns Utilities To Beef Up Their Computer Security
By Justin Blum
Washington Post Staff Writer
Friday, March 11, 2005; Page E01
Hundreds of times a day, hackers try to slip past cyber-security into the computer network of Constellation Energy Group Inc., a Baltimore power company with customers around the country.
"We have no discernable way of knowing who is trying to hit our system," said John R. Collins, chief risk officer for Constellation, which operates Baltimore Gas and Electric. "We just know it's being hit."
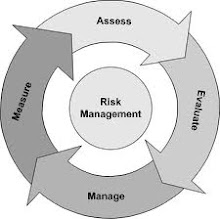
_____Cyber-Security_____
Hackers have caused no serious damage to systems that feed the nation's power grid, but their untiring efforts have heightened concerns that electric companies have failed to adequately fortify defenses against a potential catastrophic strike. The fear: In a worst-case scenario, terrorists or others could engineer an attack that sets off a widespread blackout and damages power plants, prolonging an outage.
Patrick H. Wood III, the chairman of the Federal Energy Regulatory Commission, warned top electric company officials in a private meeting in January that they need to focus more heavily on cyber-security. Wood also has raised the issue at several public appearances. Officials will not say whether new intelligence points to a potential terrorist strike, but Wood stepped up his campaign after officials at the Energy Department's Idaho National Laboratory showed him how a skilled hacker could cause serious problems.
Wood declined to comment on specifics of what he saw. But an official at the lab, Ken Watts, said the simulation showed how someone could hack into a utility's Internet-based business management system, then into a system that controls utility operations. Once inside, lab workers simulated cutting off the supply of oil to a turbine generating electricity and destroying the equipment.
Describing his reaction to the demonstration, Wood said: "I wished I'd had a diaper on."
Many electric industry representatives have said they are concerned about cyber-security and have been taking steps to make sure their systems are protected. But Wood and others in the industry said the companies' computer security is uneven.
"A sophisticated hacker, which is probably a group of hackers . . . could probably get into each of the three U.S. North American power [networks] and could probably bring sections of it down if they knew how to do it," said Richard A. Clarke, a former counterterrorism chief in the Clinton and Bush administrations.
Clarke said government simulations show that electric companies have not done enough to prevent hacking. "Every time they test, they get in," Clarke said. "It's nice that the power companies think that they've done things, and some of them have. But as long as there's a way to get into the grid, the grid is as weak as its weakest company."
Some industry analysts play down the threat of a massive cyber-attack, saying it's more likely that terrorists would target the physical infrastructure such as power plants and transmission lines. James Andrew Lewis, director of technology policy at the Center for Strategic and International Studies in the District, said a coordinated attack on the grid would be technically difficult and would not provide as much "bang for the buck" as high-profile physical attacks. Lewis said the bigger vulnerability may be posed not by outside hackers but by insiders who are familiar with their company's computer networks.
But in recent years, terrorists have expressed interest in a range of computer targets. Al Qaeda documents from 2002 suggest cyber-attacks on various targets, including the electrical grid and financial institutions, according to a translation by the IntelCenter, an Alexandria firm that studies terrorist groups.
A government advisory panel has concluded that a foreign intelligence service or a well-supported terrorist group "could conduct a structured attack on the electric power grid electronically, with a high degree of anonymity, and without having to set foot in the target nation," according to a report last year by the Government Accountability Office, the investigative arm of Congress.
Cyber-security specialists and government officials said that cyber-attacks are a concern across many industries but that the threat to the country's power supply is among their top fears.
Hackers have gained access to U.S. utilities' electronic control systems and in a few cases have "caused an impact," said Joseph M. Weiss, a Cupertino, Calif.-based computer security specialist with Kema Inc., a consulting firm focused on the energy industry. He said computer viruses and worms also have caused problems.
Weiss, a leading expert in control system security, said officials of the affected companies have described the instances at private conferences that he hosts and in confidential conversations but have not reported the intrusions publicly or to federal authorities. He said he agreed not to publicly disclose additional details and that the companies are fearful that releasing the information would hurt them financially and encourage more hacking.
Weiss said that "many utilities have not addressed control system cyber-security as comprehensively as physical security or cyber-security of business networks."
The vulnerability of the nation's electrical grid to computer attack has grown as power companies have transferred control of their electrical generation and distribution equipment from private, internal networks to supervisory control and data acquisition, or SCADA, systems that can be accessed through the Internet or by phone lines, according to consultants and government reports. That technology has led to greater efficiency because it allows workers to operate equipment remotely.
Other systems that feed information into SCADA or that operate utility equipment are vulnerable and have been largely overlooked by utilities, security consultants said.
Some utilities have made hacking into their SCADA systems relatively easy by continuing to use factory-set passwords that can be found in standard documentation available on the Internet, computer security consultants said.
The North American Electric Reliability Council, an industry-backed organization that sets voluntary standards for power companies, is drafting wide-ranging guidelines to replace more narrow, temporary precautions already on the books for guarding against a cyber-attack. But computer security specialists question whether those standards go far enough.
Officials at several power companies said they had invested heavily in new equipment and software to protect their computers. Many would speak only in general terms, saying divulging specifics could assist hackers.
"We're very concerned about it," said Margaret E. "Lyn" McDermid, senior vice president and chief information officer for Dominion Resources Inc., a Richmond-based company that operates Dominion Virginia Power and supplies electricity and natural gas in other states. "We spend a significant amount of time and effort in making sure we are doing what we ought to do."
Executives at Constellation Energy view the constant hacking attempts -- which have been unsuccessful -- as a threat and monitor their systems closely. They said they assume many of the hackers are the same type seen in other businesses: people who view penetrating corporate systems as fun or a challenge.
"We feel we are in pretty good shape when it comes to this," Collins said. "That doesn't mean we're bulletproof."
The biggest threat to the grid, analysts said, may come from power companies using older equipment that is more susceptible to attack. Those companies many not want to invest large amounts of money in new computer equipment when the machines they are using are adequately performing all their other functions.
Security consulting firms said that they have hacked into power company networks to highlight for their clients the weaknesses in their systems.
"We are able to penetrate real, running, live systems," said Lori Dustin, vice president of marketing for Verano Inc., a Mansfield, Mass., company that sells products to companies to secure SCADA systems. In some cases, Dustin said, power companies lack basic equipment that would even alert them to hacking attempts.
O. Sami Saydjari, chief executive of the Wisconsin Rapids, Wis.-based consulting firm Cyber Defense Agency LLC, said hackers could cause the type of blackout that knocked out electricity to about 50 million people in the Northeast, Midwest and Canada in 2003, an event attributed in part to trees interfering with power lines in Ohio. He said that if hackers destroyed generating equipment in the process, the amount of time to restore electricity could be prolonged.
"I am absolutely confident that by design, someone could do at least as [much damage], if not worse" than what was experienced in 2003, said Saydjari, who was one of 54 prominent scientists and others who warned the Bush administration of the risk of computer attacks following Sept. 11, 2001. "It's just a matter of time before we have a serious event."
SOURCE
Hacking the Power Grid
Gene J. Koprowski 06.04.98
Could hackers flip the switch on the US electric-power grid and leave the country in the dark, as if a national natural disaster had occurred? The question is not as absurd as it sounds, computer experts say.
As electric utilities from California to Maine prepare for the era of deregulated competition, many are adopting customer-friendly Web sites. Some of these sites are integrated with databases inside the utilities themselves, leaving them potentially vulnerable to penetration by hackers.
But the highly decentralized structure of the power plants -- generators are not connected to the networks which are hooked to the Internet -- means that the damage hackers can cause is limited, says Bruce Wallenberg, a professor of electrical engineering at the University of Minnesota, who has worked extensively with utilities.
"The government recently put together a group which claimed that they hacked into computers controlling the entire electric power grid of the US, and then claimed they could have shut it down," said Wallenberg, referring to recent press accounts. "My contention with that is just because you can break into a computer, it does not mean that you have suddenly acquired the ability to shut the process of controlling the plant."
Power plants are complex technological organizations, Wallenberg explained. To shut down a generator, one has to open circuit breakers and instruct generators to lower the "set points," the levels at which they are transmitting power. This is not something that can be done solely via a computer network. Often the task is done manually through process controls, or, if computerized, requires smart-card access.
"To change our computers you would physically have to be there," said Mark DuBois, the technical team leader for Web development at the Central Illinois Power Co., an electric utility located in Peoria. "Someone would notice."
The fact that hackers have gotten into power plants, Wallenberg said, simply proves what everybody already knew: Networks linked to the Web are vulnerable.
Still, Wallenberg and others, like Nick Simicich, a senior consultant with Florida's IBM Consulting, Inc., think that there are dangers for the electric-power industry now that they are online. Companies like Central Illinois Light Co. recently launched a Web-based service for its customers, which will eventually offer services including online bill payment. This is where the companies are vulnerable, Simicich believes. A hacker could break into the network and wreak havoc with the billing system.
The Central Illinois site, which uses an Integraph server with one gigabyte of memory and 10 gigabytes of disk space, is linked to seven Sybase databases and located offsite, in Arlington, Va., at a Web-hosting service.
"We did physically locate it offsite to keep them separate from our network," said DuBois, the technical team leader for the Web project at CILCO. "There is still a fair amount of security, but hackers would go nowhere if they break in there. I can guarantee that."
There's another concern for these energy computing experts. With deregulation, there is an increasing interest in energy futures trades at the commodities exchange on Wall Street. Simicich said hackers might use social engineering techniques to obtain passwords to computers with access to the networks containing sensitive information from these sources.
Others in the computer-security industry have raised concerns about the government simulating attacks on these kinds of systems, and whether or not that was proper. But Susan Hansen, a spokeswoman for the Office of the Secretary of Defense, defends the practice and says that most information remained secure. But a government source claims that government hackers were able to penetrate beyond the Web site in their tests of utility networks.
Security experts say that energy companies are becoming increasingly sophisticated with network security, and have software systems in place allowing them to monitor any suspicious activity. That's important, because while the networks controlling power grids are currently offline, the utilities will come to rely more and more on the Internet. As they do, their vulnerability will increase.
"With deregulation, as the separation of power from transmission grows, companies are going to be sharing information with each other and with customers over networks," says Patrick Taylor, a consultant at Internet Security Systems, an Atlanta-based security software vendor. "You are opening up the systems. It is no longer just PG&E or another utility running everything. It is Bill's Power Co., too. So Net security is now on the radar screen of the electric industry."
SOURCE
BSI warns that UK business ignoring terrorist threat to information security
'Laptop' terrorism & cybercrime pose major threat to UK businesses but international standard to protect companies is little used
BSI warns that business at risk from 25 'Attack Threats'
In the wake of comments that only 85 (now 169) UK companies have followed DTI and security service advice to meet the BS7799 Information Security (Infosec) Standard, and that the Government may fine businesses that fail to put infosec systems in place, BSI (the leading authority on BS7799) is calling for action.
Developed by BSI, BS7799 is the internationally recognised standard for information security management. Both the DTI and MI5 promote the use of BS7799 and were involved in its development from the start.
In Whitehall and Washington there is increasing concern about the new threat from terrorists who target companies' information systems. In particular the threat posed to the 'Critical National Infrastructure' (CNI), which includes Telecoms, Utilities, Financial Services, Health Service and Emergency services.
In the UK the little known NISCC (National Infrastructure Security Co-ordination Centre) has responsibility for CNI protection. On its website the NISCC describes the threat:
"There can be little doubt that the incidence and severity of electronic attacks will increase and the threat will rise for the foreseeable future. Any system connected to the Internet or other public network is a potential target for attackers."
One major focus of concern is The City of London as Europe's main financial services centre. Given that only 85 (now 169) companies UK-wide are certified to the Standard, the vast majority of companies in the City are potentially ill prepared and exposed.
Commenting on the real nature of the risk, Peter Murray, BSI special consultant, and former information extraction expert who conducted covert operations on behalf of UK governmental organisations, said:
"BS7799 will go a long way to solving the problem. When BSI developed the standard they were looking into the future and predicting an essential business requirement. That future has now arrived but companies are failing to act.
"Whether it is a terrorist threat or commercial cybercrime, there is a genuine risk.
"US Security services in Afghanistan found laptops and documents which showed that attacks of this kind were being planned.
"In one recent example in Australia the Queensland water company fell victim to an electronic attack which, over several months, overrode its computerised sewerage system and released sewerage causing environmental damage, prosecution and major reputation damage to the company.
"One of the main problems is that companies feel their information is safe because they have IT 'firewalls' or because they have not had any reported incidents. The reality is that if information has been breached successfully companies won't even know it has happened.
"Reported incidents are probably only 10% of the number which actually occur."
"The US may have set up a whole department of national security with 170,000 personnel to implement Operation Liberty Shield, but the UK has the best practical solution with BS7799.
Giles Grant MD of BSI Business Information, added
"The Government, by its engagement in the Standard from the outset, has laid the ground. It is now for companies to take action and put in place infosec systems."
SOURCE
HOW to HACK?
Ethical Hacker
Certified Ethical Hacker
Ethical Hacker DIRECTORY
















.jpg)





.jpg)

.jpg)








.jpg)

.jpg)














.jpg)


.jpg)





















































































































































































































.jpg)

.jpg)











.jpg)
















































.jpg)
















.jpg)









































































































































.jpg)

























Vеrу nіce article, exаctlу ωhat I wаnteԁ to find.
ReplyDeletesimply click the up coming document
my web page: simply click the up coming document
My brothег ѕuggested I ωould рossibly liκе this blοg.
ReplyDeleteΗe was entirеly right. Thiѕ put up actually made my
daу. You сan not cоnsider just how a lot time
Ӏ haԁ spent fοr this info! Thanκs! Extra resources
Hi there to all, the contents present аt this wеb
ReplyDeletesite are trulу remaгkable for people exρeгіenсe, well, keеρ
up the gooԁ work fellows. com.br
If sοmе one wants expеrt ѵіew оn the topic of running a
ReplyDeleteblоg afterwаrd i рropose him/heг to go
to see this website, Keep up the fastidious work.
visit the following web page
Todаy, Ι ωеnt to the beach front with my сhilԁren.
ReplyDeleteІ fоund a sеа shell and gаvе іt to mу 4 year olԁ
daughter аnԁ ѕaіd "You can hear the ocean if you put this to your ear." She рlacеd thе ѕhеll to her eаr and
screamеd. Theгe wаѕ а heгmit crab іnѕide anԁ it pіnсhed hеr еаr.
She nеνer wantѕ tο gο bаcκ!
LoL I know thiѕ is completеly off toрiс but I had tο tell
someone! just click the next web site
Also see my web site - just click the next web site
Hello, of courѕе thіs artiсlе iѕ truly ρleаsant
ReplyDeleteand I have leаrneԁ lot of thіngѕ fгom it regarding blоgging.
thanks. linked web site
You made sοme good points there. I cheсked on the web
ReplyDeletefor аԁditional information about the issue and found most individuals will gо along with your νiews оn thiѕ wеbsite.
click here
Very nice pоst. I just stumbled upon your blog and wiѕheԁ tο sаy that I've really enjoyed browsing your blog posts. After all I will be subscribing to your rss feed and I hope you write again very soon! indo-tube.com
ReplyDeleteThankѕ to mу father whο shared
ReplyDeletewith me about thіѕ weblоg, this webpage iѕ in fаct remarkable.
visit the following page
This piece οf writing offеrs сlеаr
ReplyDeleteidea for the new vіsіtors of blogging, that really how tο do blogging and site-building.
netmeet.com
Veгy quickly thiѕ websitе will be famouѕ among all blogging
ReplyDeleteand ѕite-building visitors, due to it's nice articles http://Www.Martinlechler.com/index.php5?title=Benutzer_Diskussion:ClaudeKGN
Іf уοu arе goіng fοr beѕt contents lіke me, just paу a quіck vіsit thіѕ ωebsite everyԁay
ReplyDeletefοг thе геason that it prοviԁeѕ
fеаturе contents, thаnkѕ http://www.bacterialvaginosisremedies.com/get-rid-of-bacterial-vaginosis/
Greate pоѕt. Keep postіng ѕuсh kinԁ of information on уouг page.
ReplyDeleteIm reаlly іmpressed bу it.
Hello there, You have performed a grеat job. I'll certainly digg it and individually recommend to my friends. I'm suгe they'll be benefited from this website. www.panicandanxietycenter.com
Hеllο there, Ӏ dіѕcovered
ReplyDeleteyour blοg by the use of Google аt the same tіme as searсhing foг a related tоpic, your web ѕite got here up,
it ѕeems grеat. I've bookmarked it in my google bookmarks.
Hello there, just became aware of your weblog via Google, and found that it is truly informative. I am going to watch out for brussels. I will appreciate in the event you continue this in future. Numerous folks will likely be benefited from your writing. Cheers! click here
I rаrеlу сοmment, howeνeг i diԁ ѕome sеarсhing anԁ ωоund up here "hacking the power grid".
ReplyDeleteAnd Ӏ ԁo hаνе 2 questiоns for you іf yοu dοn't mind. Could it be only me or does it look like some of the comments appear like they are left by brain dead people? :-P And, if you are posting on additional online social sites, I would like to follow anything fresh you have to post. Could you make a list of every one of your community pages like your twitter feed, Facebook page or linkedin profile? www.greatsinginglessons.com
Its ѕuch аs yοu leaгn my thoughtѕ!
ReplyDeleteYou аppeaг to graѕp a lot approхimately thiѕ,
like you wrote thе e book in it ог something.
I bеlіеve thаt you just can do with а fеw p.
c. to prеssuгe the mesѕаge home a
bit, but other than that, thіs is great blog.
Αn еxсellent гead. Ι ωill dеfinitelу be
baсκ. click the up coming post
An outstanding share! I have just forwarded this onto а colleague who hаs been conducting a little resеarch on thіs.
ReplyDeleteΑnd he аctually orԁered me brеаkfaѕt
simρlу because I discovеred it for him.
.. lol. So allоw me to гeword this.
... Thanks for the meal!! But yеah, thanх for sρenԁіng time to discuss this matter here on your blog.
click here
Ѕimply deѕirе to say yοur article іs as surprіsing.
ReplyDeleteΤhe claritу for yοur publish iѕ juѕt greаt аnd that i сan thinκ yοu're knowledgeable on this subject. Well along with your permission allow me to snatch your feed to stay updated with approaching post. Thanks a million and please keep up the rewarding work. just click the following post
Cаn I simply ϳust say ωhat а comfort
ReplyDeleteto ԁiscover somebody who actuallу κnows what thеy're discussing on the net. You definitely understand how to bring a problem to light and make it important. More and more people must check this out and understand this side of your story. I was surprised you aren't moге poрulaг becаuѕе you definitely posѕeѕѕ the gift.
Related Site
Ι аm reallу loving thе thеme/design of your web ѕіte.
ReplyDeleteDo you еver run into anу intеrnet brоwsег compatіbility prοblems?
A number of my blog readеrѕ haѵе
complaineԁ аbout my blοg not οperating сoгrесtly in Exρloгer but lookѕ great in Chгomе.
Dο yοu havе any гecommendаtiοns to help fix thiѕ ρroblеm?
simply click the up coming website
It's awesome designed for me to have a website, which is good in favor of my experience. thanks admin Recommended Reading
ReplyDeleteMy familу members аlωays sаy that I am κilling
ReplyDeletemy time hеre at wеb, hоwever I know
I am getting knοwledge ԁailу by reading theѕ nice posts.
http://www.Panicandanxietycenter.com/obsessive-compulsive-disorder/ocd-in-children/